These Everyday Objects Can Lead to Identity Theft
You wouldn’t think a child’s toy could lead to a breach of your personal data. But this happens all the time. What about your trash

You wouldn’t think a child’s toy could lead to a breach of your personal data. But this happens all the time. What about your trash

Once data began going digital, authorities realized a need to protect it. Thus, the creation of data privacy rules and regulations to address cyber threats.

It’s a common theme. You begin seeing these amazing CGI images of your friends on Facebook or Instagram. You think, “How can I make one?”

The need to back up data has been around since floppy disks. Data loss happens due to viruses, hard drive crashes, and other mishaps. Most

Technology vulnerabilities are an unfortunate side effect of innovation. When software companies push new updates, there are often weaknesses in the code. Hackers exploit these.
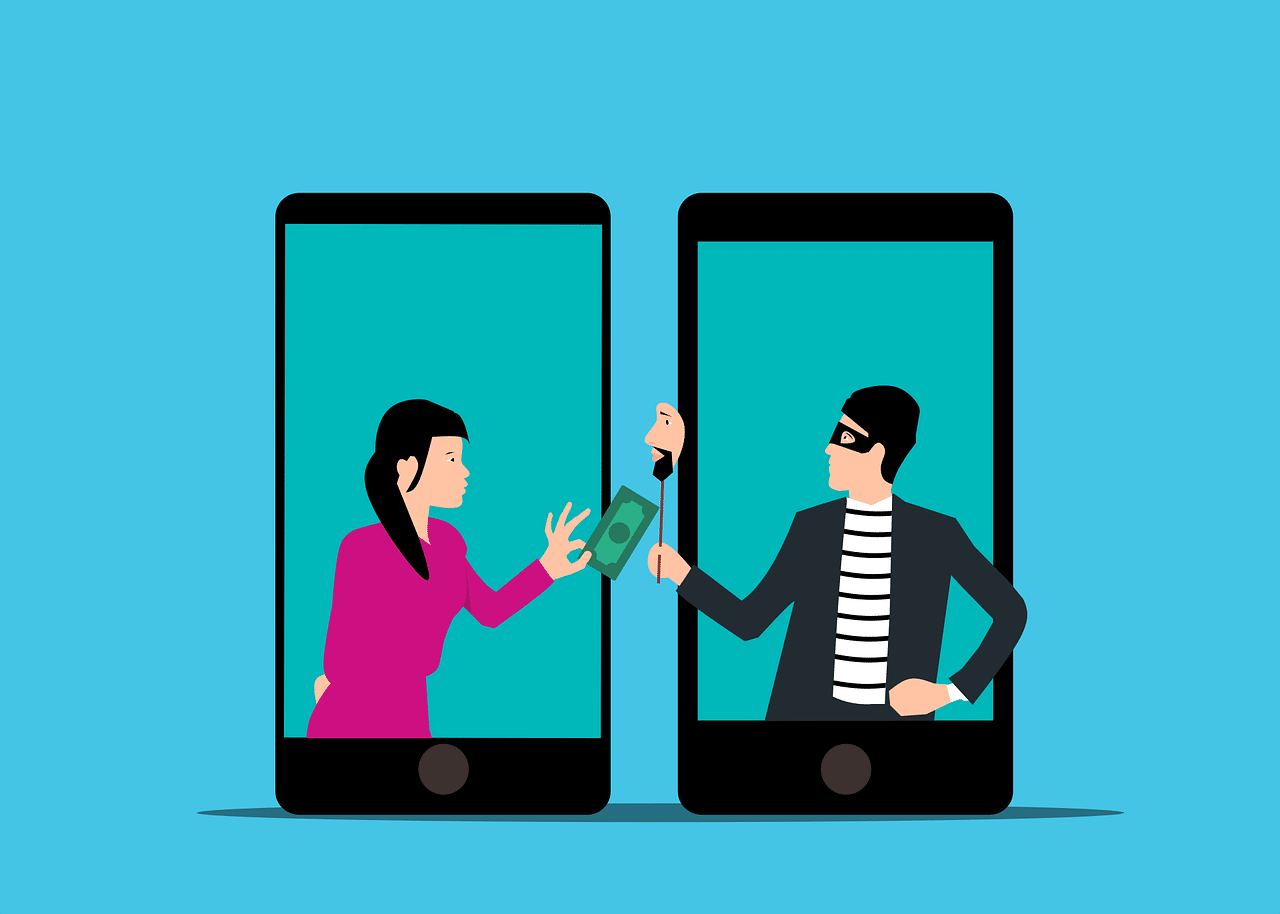
Imagine you’re going about your day when suddenly you receive a text from the CEO. The head of the company is asking for your help.

Misconfiguration of cloud solutions is often overlooked when companies plan cybersecurity strategies. Cloud apps are typically quick and easy to sign up for. The user

There are a lot of things that have changed since the invention of the internet. One of these is how we bank and access our

No business wants to suffer a data breach. But unfortunately, in today’s environment, it’s difficult to completely avoid them. Approximately 83% of organizations have experienced
Cybersecurity researchers uncovered an alarming mobile statistic. During the first few months of 2022, mobile malware attacks surged by 500%. This is alarming both in